-3.png)
-3.png)
Learn which methods of protection you should use and how to create a ransomware-ready recovery plan
We will be careful with your email address. Please review our Privacy Policy.
-3.png)
-3.png)
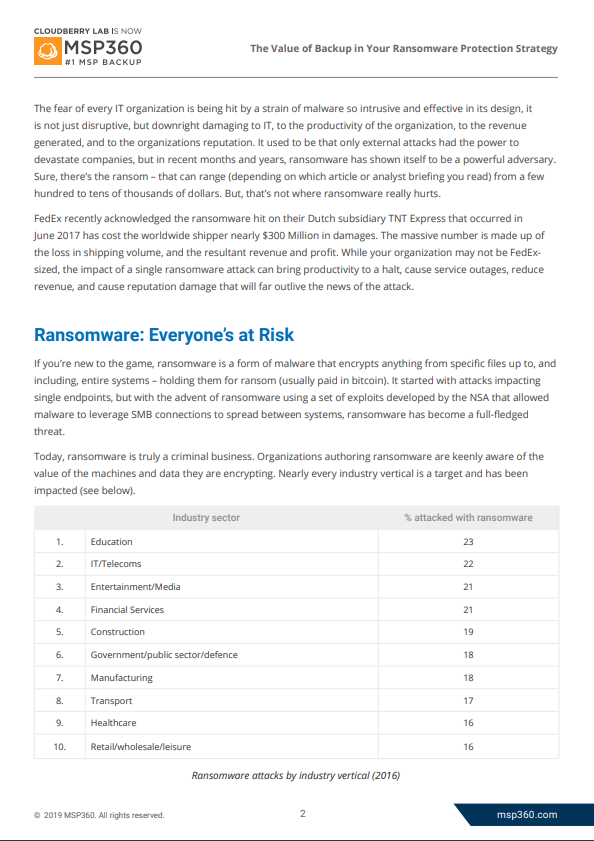
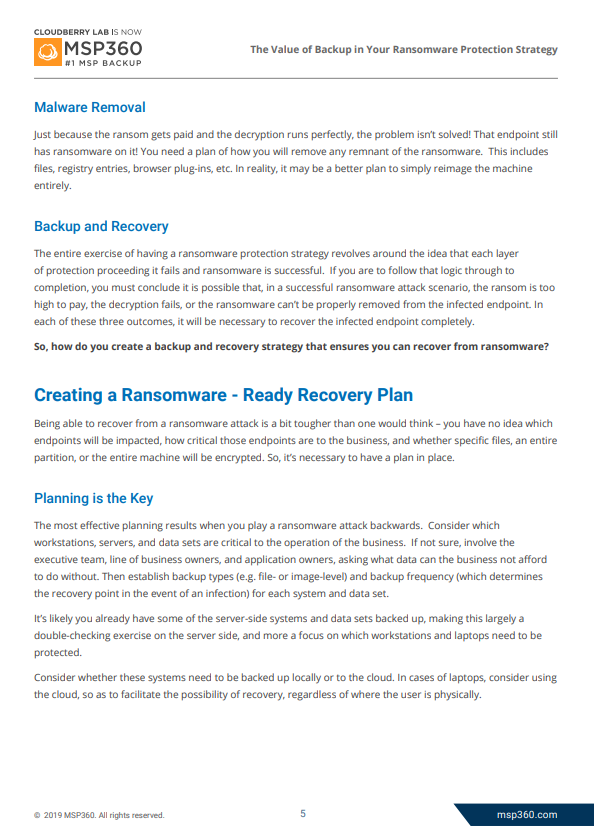
In this whitepaper, we explain what your ransomware protection strategy should look like, highlighting the value of having a solid backup and recovery plan to ensure you can get the organization back into a state of operation as quickly as possible.
We discuss: